



grKey manages access to your critical infrastructure.
Critical business data or infrastructures are only accessible to administrators. Getting administrator accounts and passwords allows unrestricted access to all networks and systems. grKey affords extensive granular control of accesses, to balance usage with necessary cyber protection for qualitative governance.
Managing administrators’ credentials and access rights require extensive knowledge and efforts. Our integrated platform in our MDR allows for our staff to manage the platform on your behalf, taking away the burden of maintaining knowledge and security expertise while ensuring smooth operations.
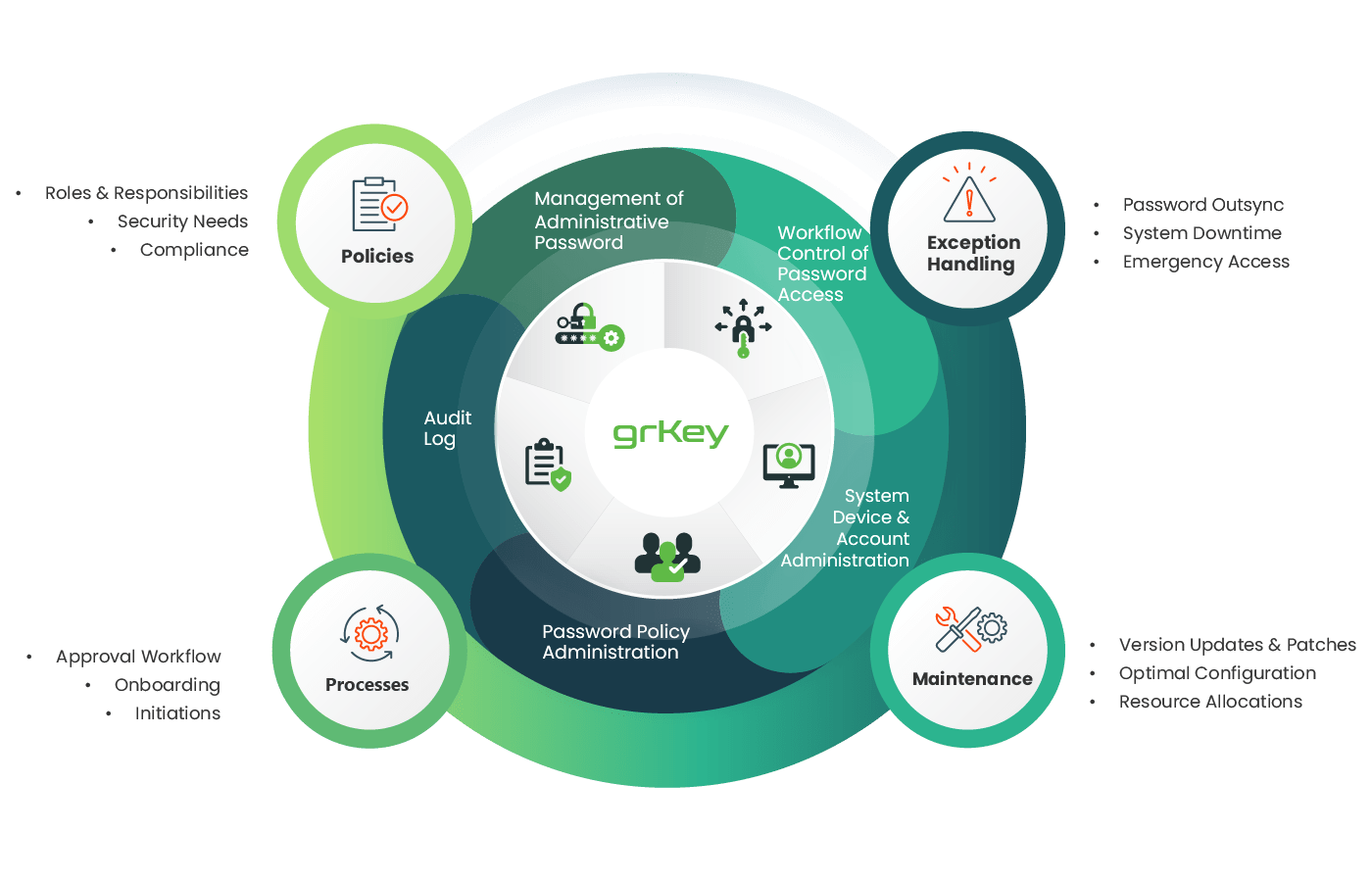
grKey offers rich functionalities for an organization to manage administration access and credentials, include regular change of administration passwords and workflow approval of access to controlled systems.
grKey is designed to bring up visibility and accountability so that policy stickiness can be measured. As such, one of the most important aspects is to ensure that the platform comes with rich interface for reporting and visibility on the privileged activities.
Managing privileged identities require strong operation support and reliable technology platform. Our secured cloud-based platform is designed with this in mind to handle the management of privileged identities in clients’ environments. grKey remotely integrates account management functions, such as password change, user access control and activity visibility with operation support to ensure smooth operation. The platform automatically and regularly updates privileged passwords, rotating expiring, or non-compliant passwords out of use and store them in secured and encrypted data keeps. Operation team ensures that exceptions are handled, as well as driving governance and adaption. This offers a complete Privileged Identity Management suite for our clients, while taking away the expensive CAPEX and OPEX to own and run your own operations.
grKey is derived from more than 15 years of extensive PIM operational experiences working with over 100 Hong Kong enterprises, ensuring locally adapted industrial best practices are made available to all our clients.
Our technology was built to specifically handle administrative account management. It is complemented by experienced operational and security teams to ensure that resources are properly governed.
With an existing SOC that had been proven with an uptime of 99.999% and certified to ISO27001. Our team knows how to ensure that service is always available, and that due processes always take place.