A new phishing campaign using “Purchase Order” as lures has been globally spotted recently while attempting to install malware that could allow bad actors to harvest sensitive info or take control ofvictims’ compromised systems.
With subject “Purchase Ordered ***ASIC***”, phisher impersonates “United Cranes & Rigging” in the email, which was found to be sent out from a compromised MailChimp account that belongs to United Cranes & Rigging company.
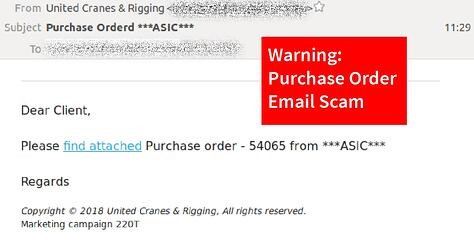
This email informed recipients of a purchase order “Please find attached Purchase order – 54065 from ***ASIC***” with a link to open the order file.
When the link is opened, it will direct users to a malicious .doc file that contains macros. The document prompts users to enable the macros if they wished to edit or view the contents. Once it is enabled, the target will unintentionally download malware and get infected.

Green Radar has also seen this same technique being used for other subjects in Singapore and Hong Kong. If you receive an email that contains links to ask you to download documents, it is strongly advised that you contact the organization by phone to confirm the email. Organizations can also be further secured by adopting email security gateway. Green Radar grMail provides a comprehensive email protection to users. In such cases, grMail can use the sandbox to examine and filter the email attachment with all hidden coding being stripped off, leaving a safe and malware-free email to our users.
Learn how Green Radar grMail protects businesses from virus, phishing and malware.
